The lifeblood of virtually every modern business is data. Without the ability to access, process, share and analyze information, organizations are unable to run efficiently, or offer the products and services that their customers really want. And the way the world of work is changing means that maintaining and securing that data has perhaps become harder than ever.
How flexible work has changed data security
In the pre-pandemic world where regimented office work was the norm, the fundamentals around data security were clear (even if the growing threat of cybercrime made the act of security far from simple). As business data was generally stored and accessed within the office building, data could reside within an on-premises data center, to which an IT team could apply and monitor all the relevant security functions needed.
However, now that flexible work is more commonplace, and employees are distributed across more locations day-to-day, this model doesn’t really work anymore. Employees need access to data whenever and wherever they’re working, and that increased freedom of data increases the exposure of that information. It is suddenly far easier for sensitive information to fall into the wrong hands – either accidentally or on purpose – and thanks to increasingly stringent regulations like GDPR in Europe and CCPA in California, the consequences of a data breach like this are severe.
All this means is that businesses must strike a balance between enabling a smooth flow of data so that flexible work is a success, while that it is as safe and secure as it possibly can be. To do so, there are (number) vital areas that organizations and their IT teams need to cover:
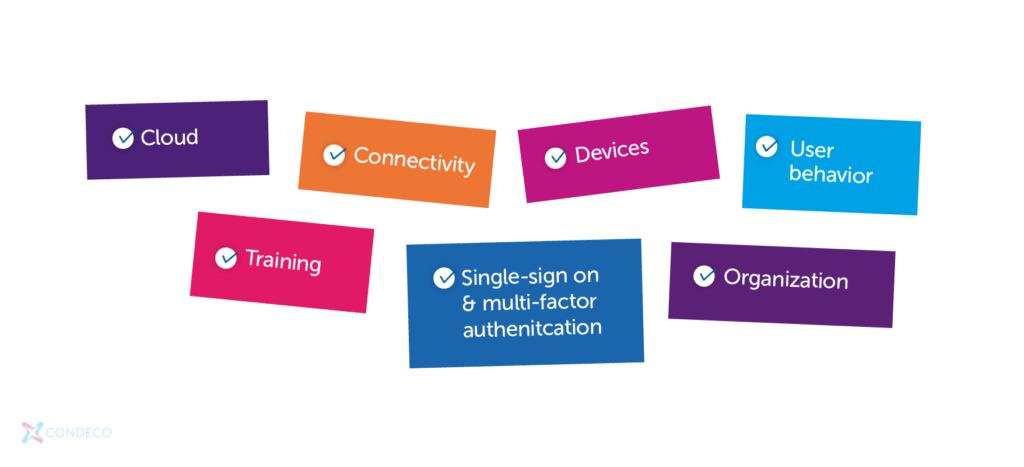
Cloud
If it hasn’t happened already, there is no time to lose in pursuing or accelerating a cloud migration. With the right cloud set-up in place, IT teams can ensure that data is held securely, and while they can give ready data access to employees wherever they’re working, IT teams are able to manage who can access what. Partnering with some of the biggest and best-resourced tech firms in the world means that a good cloud deployment also means getting the gold standard in data security.
Connectivity
Obviously, every user needs to have a reliable internet connection to do their jobs when working remotely, and to access the data and applications they need day-to-day. The potential problem arises when they’re relying on a home Wi-Fi connection, which is unlikely to have the same quality of protection as business connectivity, such as an enterprise-grade firewall. Additionally, business data could be at risk of malware or other threats generated by personal activity undertaken by an employee on the same connection.
Devices
Like the previous point, if a Bring-Your-Own-Device (BYOD) policy is in place, then employees may be using any number of their own personal devices to access business data, such as smartphones, tablets and laptops. Not only could these devices not have an adequate level of protection in place, but they are often outside of the control and monitoring of the IT team, who therefore can’t keep watch for any specific activity. Supplying business-issued devices, and/or ensuring all business activity on personal devices takes place through secure virtual sessions, is therefore critical.
User behavior
Even with the best levels of security protection in place, many data breaches happen through simple user error. Awareness of cybercrime among the general population is high, but still people often fall for phishing emails or clicking on malicious links. This may not be something that a business can eliminate completely, but it is something that can be substantially reduced through regular training and education that encourages vigilance and best practice throughout the workforce.
Tips for passwords
People will also often use the same password for everything or use an easy and insecure password for easy access. Here are a few tips for good passwords:
- Easy sequences such as QWERTY and 123456
- Avoid memorable combinations such as dates or birth
- Use a password management system so you don’t have to juggle dozens of different passwords
- Use a method such as a passphrase, which includes random multiple words
- Encourage a regular review/change of passwords every six months
Single-sign on and multi-factor authentication
SSO and MFA can add an additional layer of security. SSO involves the company having complete control over sign in, rather than having individual users create their own logins. Only one set of credentials is required. MFA is where users must enter another code in addition to their password when logging in.
Training

People may have gaps in their knowledge when it comes to IT security and may not be aware of the risks that are associated with working from home. As long as they don’t lose their laptop, it’s secure, right? A strong education around how hacking works, how easy it can be to hack passwords, and what they can do to safeguard against such data breaches. Regular training for employees – both old and new – is essential for giving data/IT security a permanent place within your company’s culture. Not only will people understand and value it, but it will also help to minimize the risk of human error.
Organization
Flexible work needs a strong workspace management and scheduling platform in place, so that everyone knows who is working where and when for collaboration, and so that employees can access the workspaces they need when they need them. Of course, such a platform will contain lots of sensitive information around how a business is operating and what employees are doing. It’s therefore crucial when evaluating any solution that businesses check that it’s underpinned by industry-leading security.